The Need for Post-Quantum Cryptography
The threat quantum computers pose to encryption is growing faster than many expected. Historically, the internet has relied on algorithms like RSA encryption and Elliptic Curve Cryptography (ECC) to exchange encryption keys and verify identities across the web. These algorithms are in danger of being entirely broken by the new capabilities of quantum computers, leaving our communications insecure. Modern breakthroughs in research are bringing us closer to this becoming a reality than we expected.
Quantum computers can be thought of as computers with fundamentally unique capabilities. Instead of using bits as memory, they use qubits. Quantum computers can run specialised “quantum algorithms” which, in some circumstances, are much faster than conventional algorithms1. RSA and ECC seemed secure when we designed them, but as we research more about quantum computers, we realise that they are not secure at all. To resolve this, we have now designed post-quantum algorithms capable of securing data even after quantum computers are accessible. NIST finalised its post-quantum standards in 2024, introducing new post-quantum algorithms such as ML-KEM to replace the old vulnerable ones.
Shor’s algorithm - the algorithm responsible for factorising the integers used in RSA encryption - has been improved and requires far fewer qubits than before. Google has also made quantum algorithms used for breaking ECC significantly more efficient. Major tech companies like Google, Microsoft, and IBM are competing to build bigger and faster quantum computers, bringing us closer to these quantum algorithms becoming possible. With these developments, the advent of quantum computing is closer than we had once expected. In response, Google has announced a 2029 timeline for using post-quantum cryptography, and Cloudflare has followed suit with their global network. It won’t be long until other major providers follow.
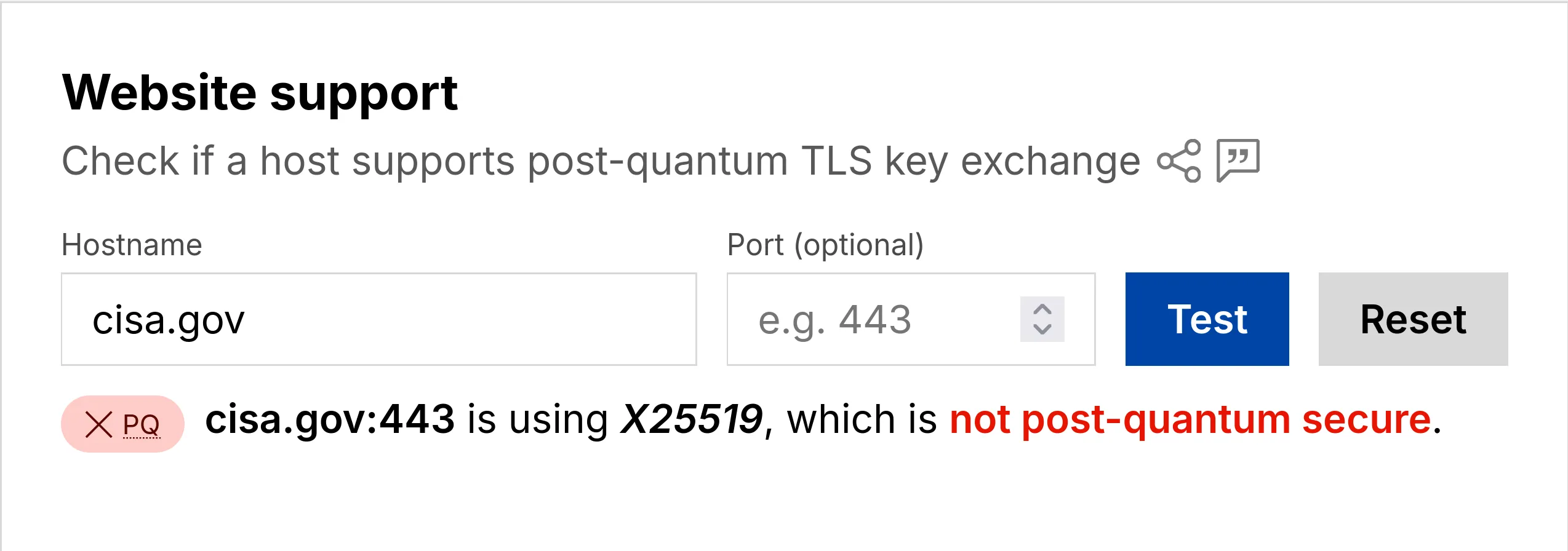
In the course of researching this, I discovered that America’s Cybersecurity and Infrastructure Security Agency surprisingly still doesn’t support post-quantum cryptography. If you want to check some websites yourself, Cloudflare offers a free tool where you can enter any URL and check.
The Risks
Adversaries aren’t waiting, even though experts in the field predict that quantum computers capable of breaking RSA are likely to be built in 10-15 years. They are already harvesting huge quantities of our encrypted communications - known as Harvest Now, Decrypt Later (HNDL) attacks - knowing they will be able to decrypt them later.
Adversaries aren’t selective, they are collecting all the data they can get their hands on. Once quantum computers arrive, they’ll decide what’s worth decrypting. The question is simply whether your data will still matter in ten years.
On a personal level, private messages, account records, medical records, and biometrics are in danger of being exposed. Some sensitive data, like passport pages and credit card details, will likely have expired by then, so there isn’t much risk for those.
For companies, trade secrets, source code, internal logs, and customer data pose great risk. Exposure of client information could lead to legal fines, and trade secrets risk losing your competitive advantage.
With governments, however, the stakes are highest. Foreign intelligence, real identities of agents in the field, military plans, and diplomatic communications are severe threats to national security.
No matter the scale you operate at, the transition needs to happen before quantum hardware catches up. That window is narrowing.
Footnotes
-
If you’re interested in more details about how quantum computing works on a fundamental level, I highly recommend the quantum.country essay, which goes into far greater depth. ↩